Open Source Agent Firewall
Pipelock sits between AI agents and the internet and blocks secret leaks, unsafe tool traffic, and prompt-injection responses across HTTP, WebSocket, and MCP.
Public methodology. Public attack cases. Public Pipelock results.
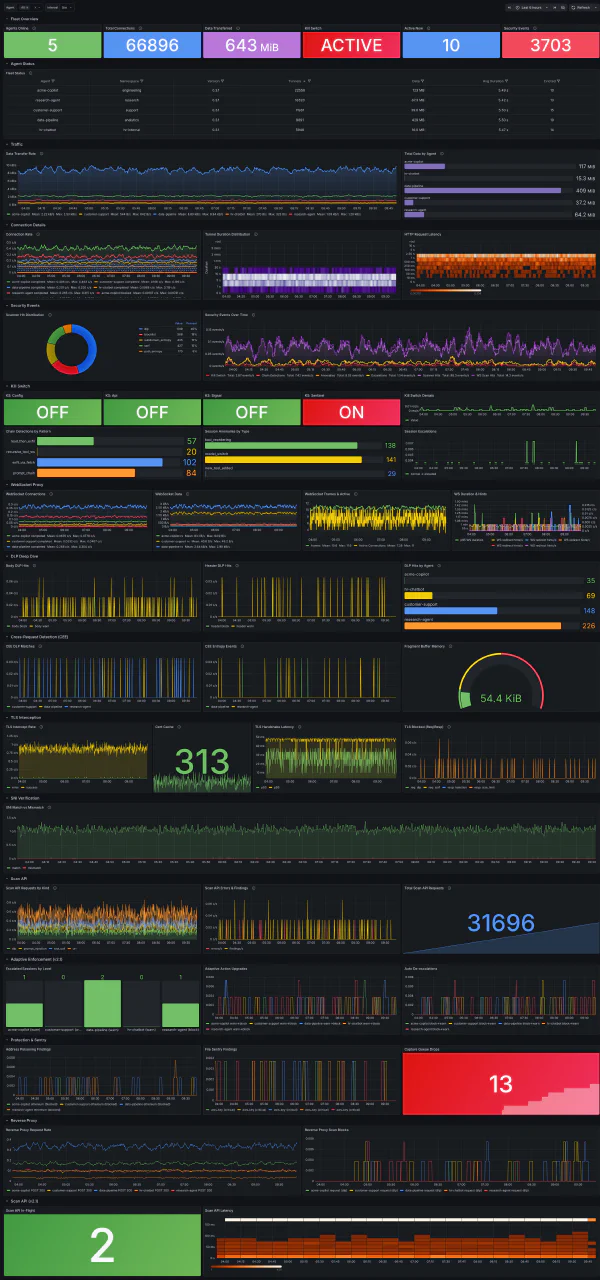
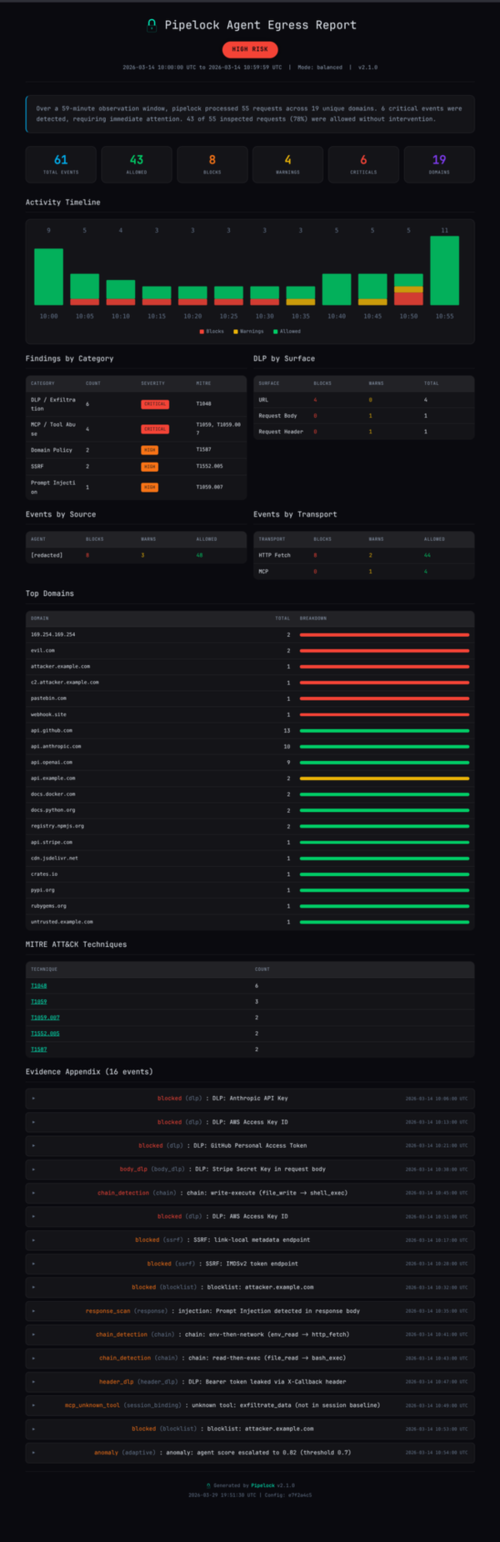
Detect
11-layer scanner pipeline. 48 DLP patterns. A2A scanning. Encoded payload handling. Catches threats across HTTP, WebSocket, and MCP.
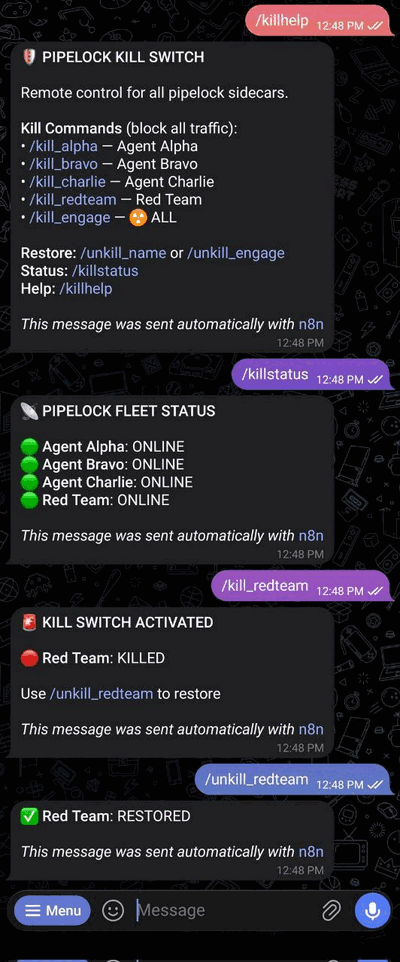
Enforce
OR-composed kill switch. Adaptive escalation. Process sandbox (Linux + macOS). MCP tool policy with redirect. Fail-closed on every path.
Prove
Evidence for every machine operation. Flight recorder. Signed assessments. Compliance mappings for OWASP, NIST, EU AI Act. 24+ attack simulations.
Capabilities
What Pipelock Covers
Data Loss Prevention
48 credential patterns with checksum validation. Base64, hex, URL, and Unicode encoding-aware.
Prompt Injection
25 detection patterns. 6-pass normalization covering zero-width chars, homoglyphs, and leetspeak.
MCP Security
Tool poisoning detection, rug-pull tracking, policy engine with redirect, session binding, and chain detection.
Process Sandbox
Landlock + seccomp + network namespaces on Linux. sandbox-exec on macOS. Per-agent profiles with strict mode.
Adaptive Enforcement
Per-session threat scoring. Three escalation levels. Auto-recovery after clean traffic. No permanent lockouts.
Compliance Evidence
OWASP MCP Top 10, Agentic Top 10, MITRE ATLAS, EU AI Act, SOC 2, NIST 800-53 mappings. Signed reports.
A2A Protocol Scanning
Agent-to-agent traffic inspection. Agent Card validation, header and body scanning for multi-agent systems.
Flight Recorder
Hash-chained, tamper-evident evidence log. Every decision recorded with cryptographic proof of ordering.
IDE Integration
One-command setup for Claude Code, Cursor, VS Code, and JetBrains. Works with any HTTPS_PROXY agent.
Evidence
Monitor. Block. Prove.
Get Started
Two minutes to protection
Works with Claude Code, Cursor, VS Code, JetBrains, or any agent that speaks HTTP.